Action Message Format (AMF) is one of the communication protocols used to exchange messages between Flash client and server; the others are RTMP and XML. BurpAMFDSer is another Burp plugin that will deserialize/serialize AMF request and response to and from XML with the use of Xtream library (https://xstream.codehaus.org/). BurpAMFDSer also utilizes part of Kenneth Hill’s Jmeter source code for custom AMF deserialization (https://github.com/steeltomato/jmeter-amf).
How to run:
java -classpath burp.jar;burpAMFDser.jar;xstream-1.4.2.jar burp.StartBurp
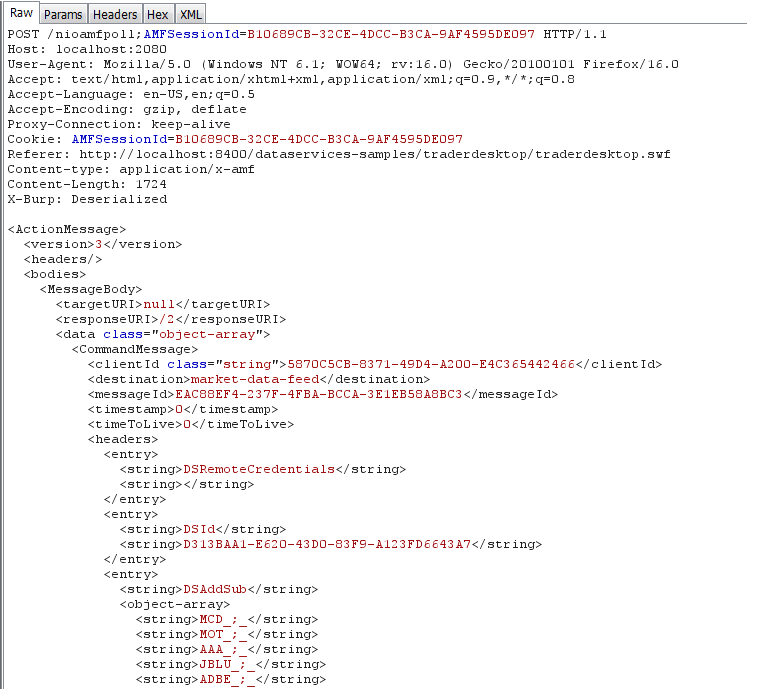
Sample serialized Request:
Sample deserialized Request:
Sample deserialized Response:
Source code and executables are available at:
https://github.com/NetSPI/burp-plugins/tree/master/BurpAMFDSer/Old_APIs
The sample application in the screenshot is TraderDesktop, provided as part of ADEP Data Services for Java EE 4.6 and could be downloaded at: https://www.adobe.com/cfusion/tdrc/index.cfm?product=livecycle_dataservices
I’ve also developed a newer version of this plugin to be compatible with the new Burp Extender APIs (https://blog.portswigger.net/2012/12/draft-new-extensibility-api.html). Now you can modify AMF requests and responses in a separate tab.
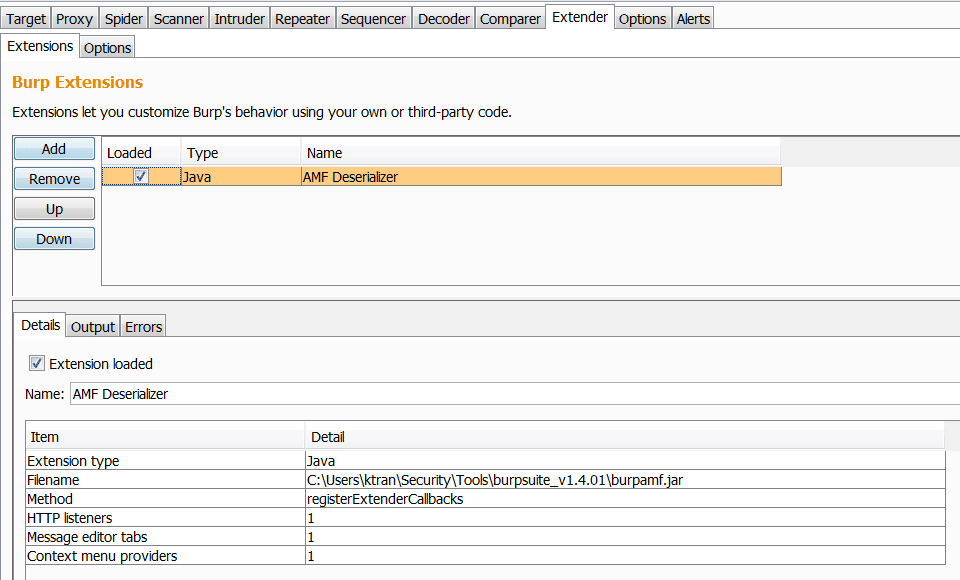
The new plugin can be loaded dynamically via Burp Extender:
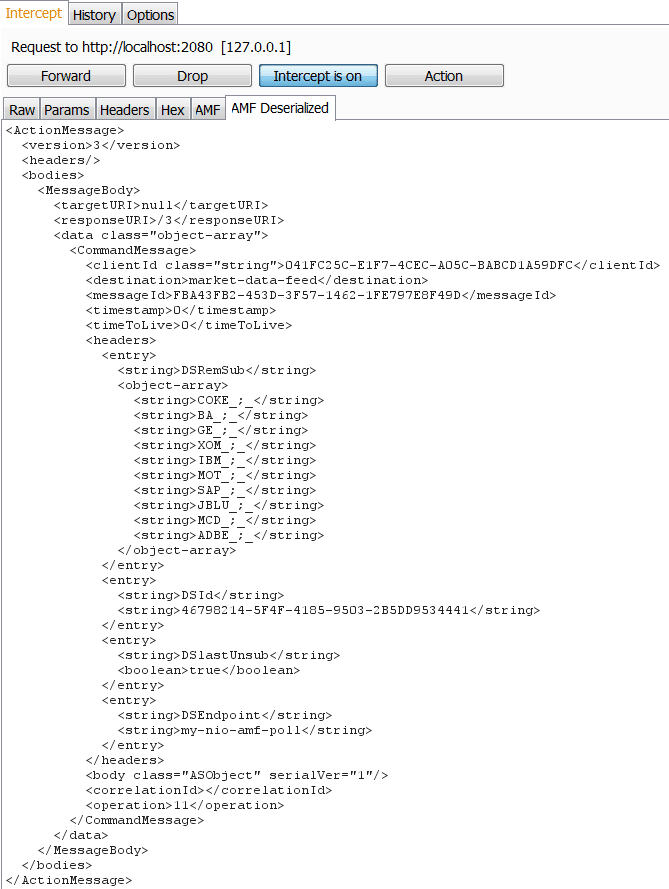
Sample Request:
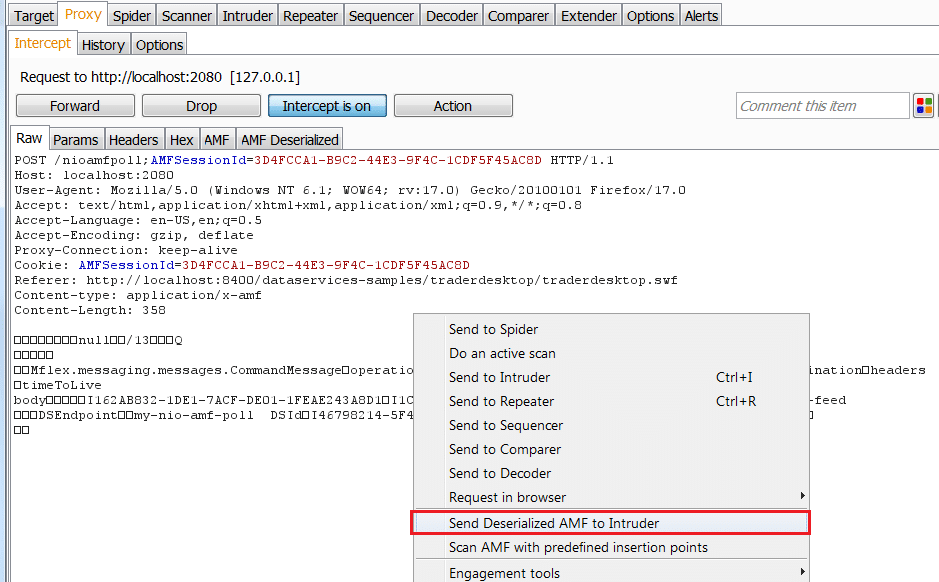
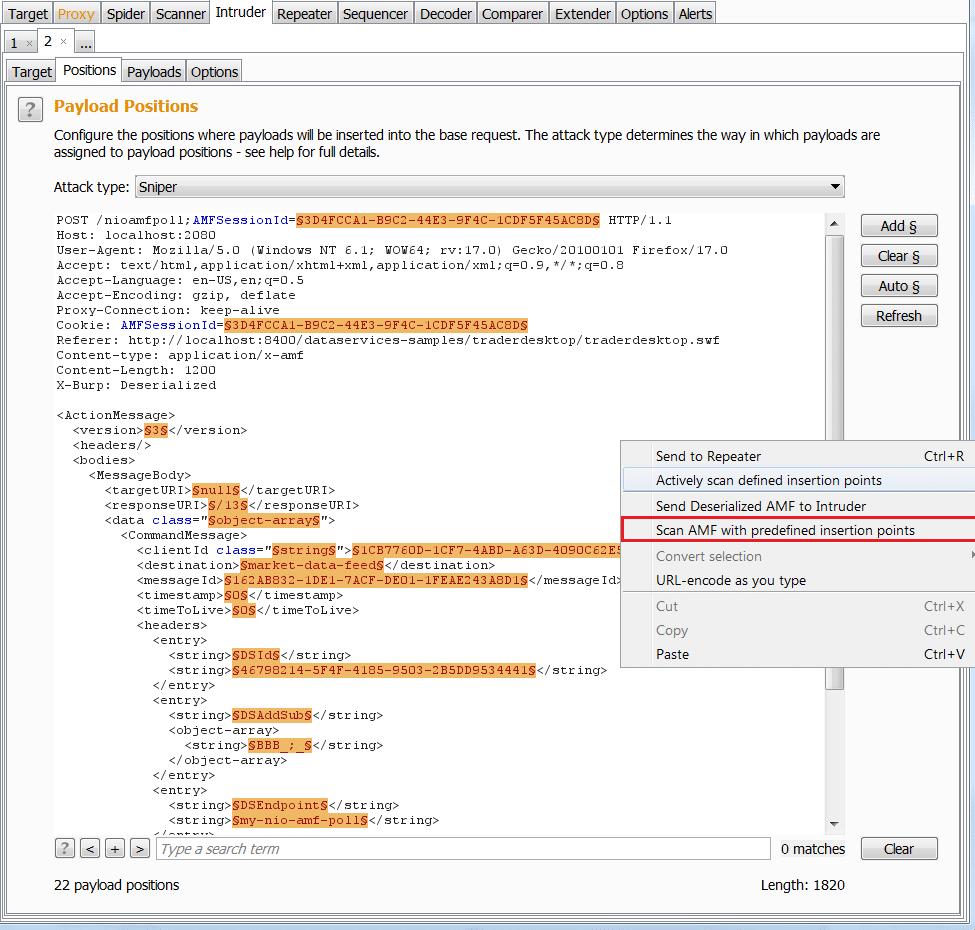
I also added 2 new menus to work with Intruder and Scanner (pro version only)
Send deserialized request to Intruder
Scan AMF (Pro version only)
Unfortunately, the new APIs are only available for Burp Suite Pro version 1.5.01 and later. Hopefully the author will update the free version soon.
If you are interested, source code and executable are available at: https://github.com/NetSPI/burp-plugins/tree/master/BurpAMFDSer/New_APIs
Explore More Blog Posts
Walking Through an Attack Path with ForceHound
In Part 2 of the series, Weylon covers how to use ForceHound to visualize Salesforce attack paths in BloodHound CE, identify transitive privilege escalation, and legacy Connected App exposures.
Auditing Salesforce Permission Hierarchies with ForceHound
Discover how ForceHound automates the collection of profiles, permission sets, and connected apps to reveal the true trust boundaries of your Salesforce organization.

Q1 2026 Critical Vulnerability Roundup: Mitigating Risk
Discover the top critical vulnerabilities of 2026 identified by Team NetSPI and learn how proactive security measures can protect your strategic business initiatives.